New TOITOIN Banking Trojan is Targeting Latin American Businesses
Since May 2023, a newly developed banking trojan named TOITOIN has been focusing on businesses that function within the Latin American (LATAM) region and operate on Windows.
“This sophisticated campaign employs a trojan that follows a multi-staged infection chain, utilizing specially crafted modules throughout each stage,” Researchers Preet Kamal and Niraj Shivtarkar who work for Zscaler stated in a report released this past week.
“These modules are custom designed to carry out malicious activities, such as injecting harmful code into remote processes, circumventing User Account Control via COM Elevation Moniker, and evading detection by Sandboxes through clever techniques like system reboots and parent process checks,” the researchers wrote.
The attempt consists of six phases and displays all the characteristics of a skillfully executed assault plan, commencing with a phishing email that contains a URL embedded into it that directs to a compressed file stored on an Amazon EC2 server to avoid detection based on domain.
The email communications exploit a bait related to invoices to deceive unsuspecting individuals into accessing them, thus triggering the contamination. Inside the compressed file is a downloading program designed to establish continuity using a shortcut file in the Windows Boot folder and connect with a distant server to obtain six subsequent payloads as MP3 files.
The person who downloads is also accountable for creating a Batch code that reboots the system after a 10-second delay. This is performed in order to “evade sandbox detection since the malicious actions occur only after the reboot,” according to researchers.
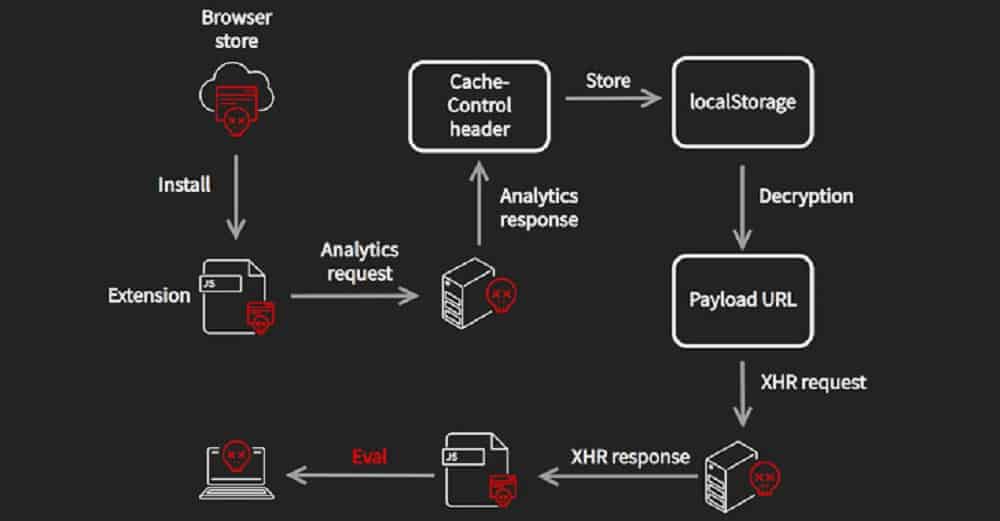
Among the obtained payloads, there is “icepdfeditor.exe,” a legitimate signed executable created by ZOHO Corporation Private Limited. When activated, it loads an unauthorized DLL (“ffmpeg.dll”) known as the Krita Loader.

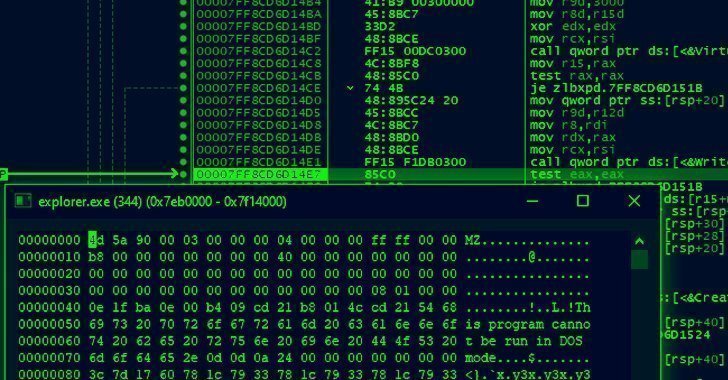
The loader is created to decipher a JPG file acquired simultaneously with the other payloads and initiate a different executable recognized as the InjectorDLL component that reverses a separate JPG file to construct what is referred to as the ElevateInjectorDLL component.
The InjectorDLL part later transfers to infuse ElevateInjectorDLL into the “explorer.exe” operation, then a User Account Control (UAC) bypass is performed, if necessary, to enhance priviliges of the process and decrypt the TOITOIN Trojan, then infuse it into the “svchost.exe” operation.
“This technique allows the malware to manipulate system files and execute commands with elevated privileges, facilitating further malicious activities,” the researchers’ report noted.
TOITOIN has the ability to collect details about the system and extract information from web browsers like Google Chrome, Microsoft Edge, Opera, Mozilla Firefox, Internet Explorer, and Opera. Additionally, it verifies the existence of Topaz Online Fraud Detection, or (OFD), a fraud prevention component incorporated into banking systems in the LATAM areas.
The current state of understanding about the responses from the command-and-control (C2) server remains uncertain because the server is currently inaccessible.
According to researchers “Through deceptive phishing emails, intricate redirect mechanisms, and domain diversification, the threat actors successfully deliver their malicious payload. The multi-staged infection chain observed in this campaign involves the use of custom-developed modules that employ various evasion techniques and encryption methods.”